SAP on Azure | Security | Identity and Access Management (IAM)
Azure Security: Identity and Access Management
In 2020, technical solutions and cloud security services are among the greatest security challenges concerning the cloud. Available are resources and services secured by design and updated automatically, however. High availability is no longer a complex task and DDoS protection runs by default.
These great advantages notwithstanding, security in the cloud is negatively affected by lack of visibility, rapidly changing workloads and infrastructures, sophisticated attacks and shortages in the security workforce.
Without visibility and a unified security management system you won’t be able to meet the security challenges of 2020. The risk of becoming compromised is omnipresent: Once under attack, you will no longer be able to provide services for your organization or customers – and you will pay the price.
To face this challenge, Microsoft Azure provides a powerful, centralized Security Management System for reinforcing your security levels: the Azure Security Center.
Azure Security Center
The Azure Security Center is a standard component, or default element, of Azure and provides unified security management and visibility. It identifies and fixes misconfigurations, summarizes the security status of your resources and issues an alert should malicious threats appear. The Center covers the protection of resources in the cloud and on-premises so that you can also protect your hybrid cloud infrastructures.
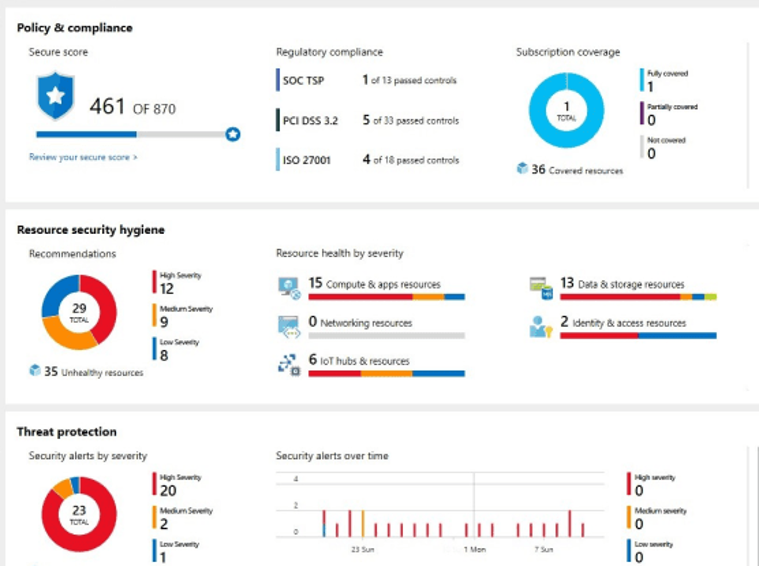
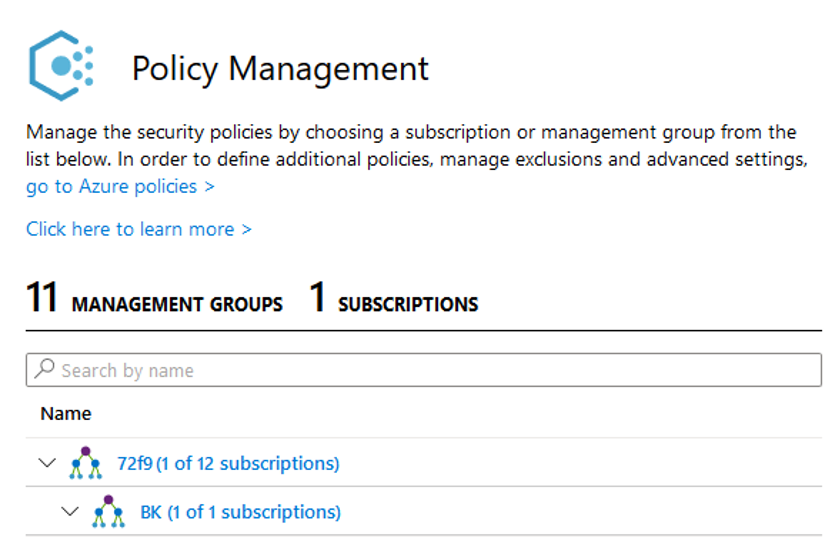
Another great feature is the management of organizational security policies and compliance. You can identify shadow IT resources and monitor compliance and governance over time.
Best practices and recommendations based on your workloads appear on top and afford you the opportunity of optimizing and improving your security. A security droid, so to speak, will be working for you.
In sum, the Azure Security Center provides visibility and analytics. But now you might ask yourself: “Where are the other thread protection elements like hunting, investigation and responding?”
No worries, these features are included – with Azure Sentinel.
With the introduction of Cloud Computing, on-premises security concepts and technologies became obsolete. At first sight, the changes and new challenges seem stressful and overwhelming. People must be trained and a new mindset must be reached. With these Best Practices, you are prepared to manage the challenges and to perform your first steps to secure the new first line of defense. Microsoft Azure provides a great toolset to reach your goal to protect and manage your identities!
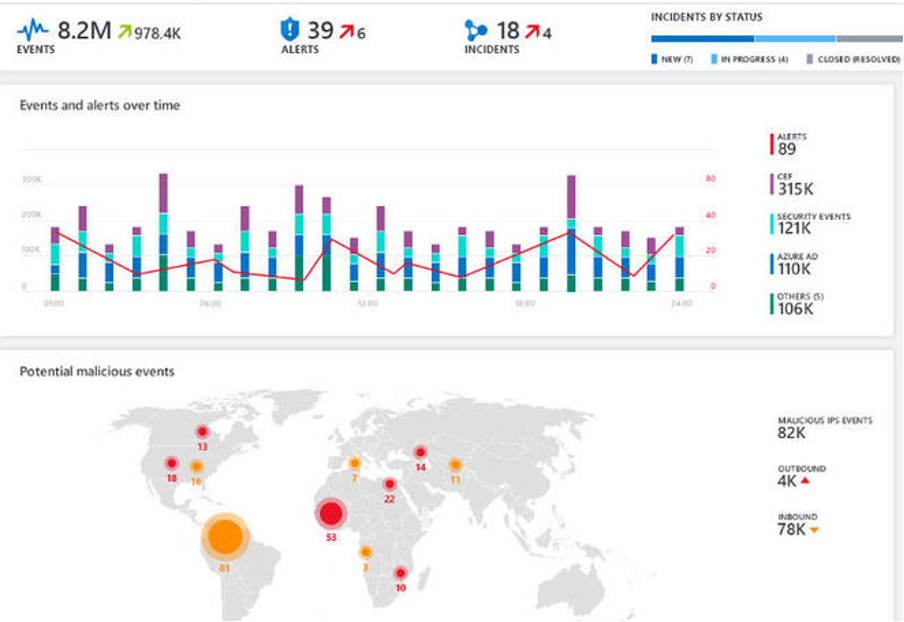
Azure Sentinel…
- collects data at cloud scale (both on-premises and in multiple clouds)
- detects previously undetected threats
- employs artificial intelligence to investigate threats
- rapidly responds to incidents
In summary, Azure sentinel enables you to keep your environment safe. Apart from the Security Center, Azure Sentinel provides additional options for digging deeper and correlating events, logs and actions in order to detect complex attacks.
The Rule of Two
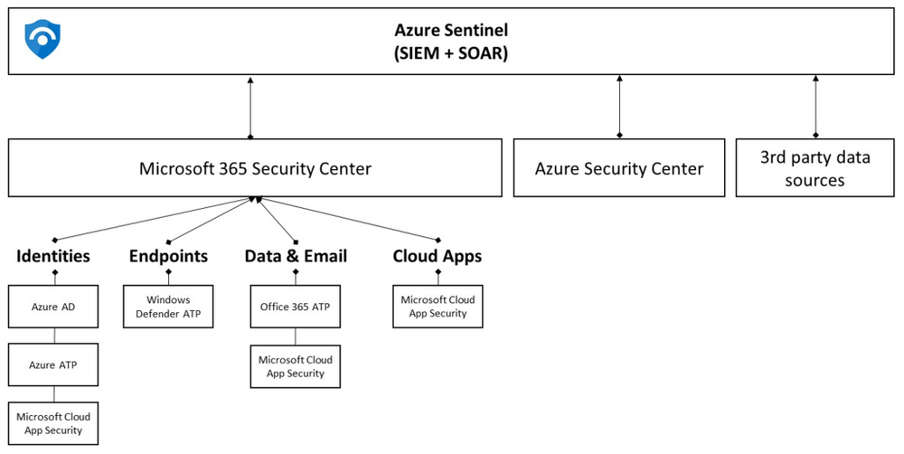
We recommend using Azure Security Center and Azure Sentinel side by side.
Use the Azure Security Center for threat protection of workloads and connect the Center to Azure Sentinel.
Once the two are connected, you’ll be able to combine data with sources in order to perform proactive threat hunting and threat mitigation.
The full power of Threat Protection on Azure will then be unleashed!
Contact: Gerard van Gent, Senior Service Manager Azure Scheer Nederland BV
This knowledge article is based on a blog by Dominic Iselt, IT Security Engineer, published earlier on the site of Scheer GmbH
